The New Frontline: Your Data
For European businesses, data ownership is no longer a theoretical compliance checkbox—it's a fundamental survival strategy.
Many European enterprises face a painful paradox: they desperately need the computational power of large AI models to remain competitive on the global stage, but using the default public models risks exposing their most valuable asset—proprietary business data—to foreign jurisdictions and competitors. The geopolitical landscape has shifted dramatically, transforming data protection from an IT security consideration to a critical boardroom priority.
The Privacy Paradox in Enterprise AI (Problem Breakdown)
The speed at which generative AI has penetrated the enterprise is unprecedented, but it has created a massive compliance and security vacuum.
The Opportunity:
- 10-10px efficiency gains in standard knowledge work
- The unprecedented ability to process unstructured data at scale
- Maintaining competitive parity with US and Asian competitors
The Threat:
- Data transmitted to US-based cloud providers may be subject to the US CLOUD Act, potentially exposing European trade secrets to foreign intelligence or competitors under certain legal frameworks.
- Training data policies for public AI models are opaque, frequently updated, and extremely difficult to audit.
- GDPR compliance becomes exponentially more complex when PII (Personally Identifiable Information) is processed by external AI models across different jurisdictions.
When an employee paste a client's financial details into a public AI chatbot to "summarize the quarterly results," that data has officially left the building. According to Eurobarometer's 2024 Digital Sovereignty Survey, 67% of European business leaders cite data sovereignty as a top-three concern, yet many still turn a blind eye to "shadow AI" usage within their ranks.
What Drives the Exposure: The Root Causes
Why is enterprise data so vulnerable in the era of Artificial Intelligence? The root causes stem from how the AI industry is currently structured and how legacy IT policies fail to grasp the mechanics of Large Language Models.
1. The "Default to Train" Business Model
The rapid advancement of AI models requires astronomical amounts of training data. As a result, many consumer and even some "business" tiers of AI services default to utilizing user inputs for model training. While opt-outs exist, they are often buried in complex settings and terms of service that change without explicit warning.
2. Trans-Atlantic Jurisdictional Conflicts
US-based cloud providers are subject to US legal authority regardless of where the data is physically stored in Europe. The tension between European GDPR requirements and US data access laws creates a legal gray area that most European enterprises are ill-equipped to navigate. If an AI provider’s servers are subpoenaed, European data could be exposed.
3. The Lack of Internal AI Tunnels
Because companies have not provided secure, internal AI tools to their employees, staff inevitably default to public tools to get their jobs done faster. This lack of secure infrastructure guarantees that sensitive intellectual property will leak outside the organization's perimeter.
Securing Your Borders: Practical Solutions
You do not have to choose between adopting cutting-edge AI and protecting your intellectual property. The solution lies in building isolated, sovereign infrastructure.
The Sovereign Gateway Architecture
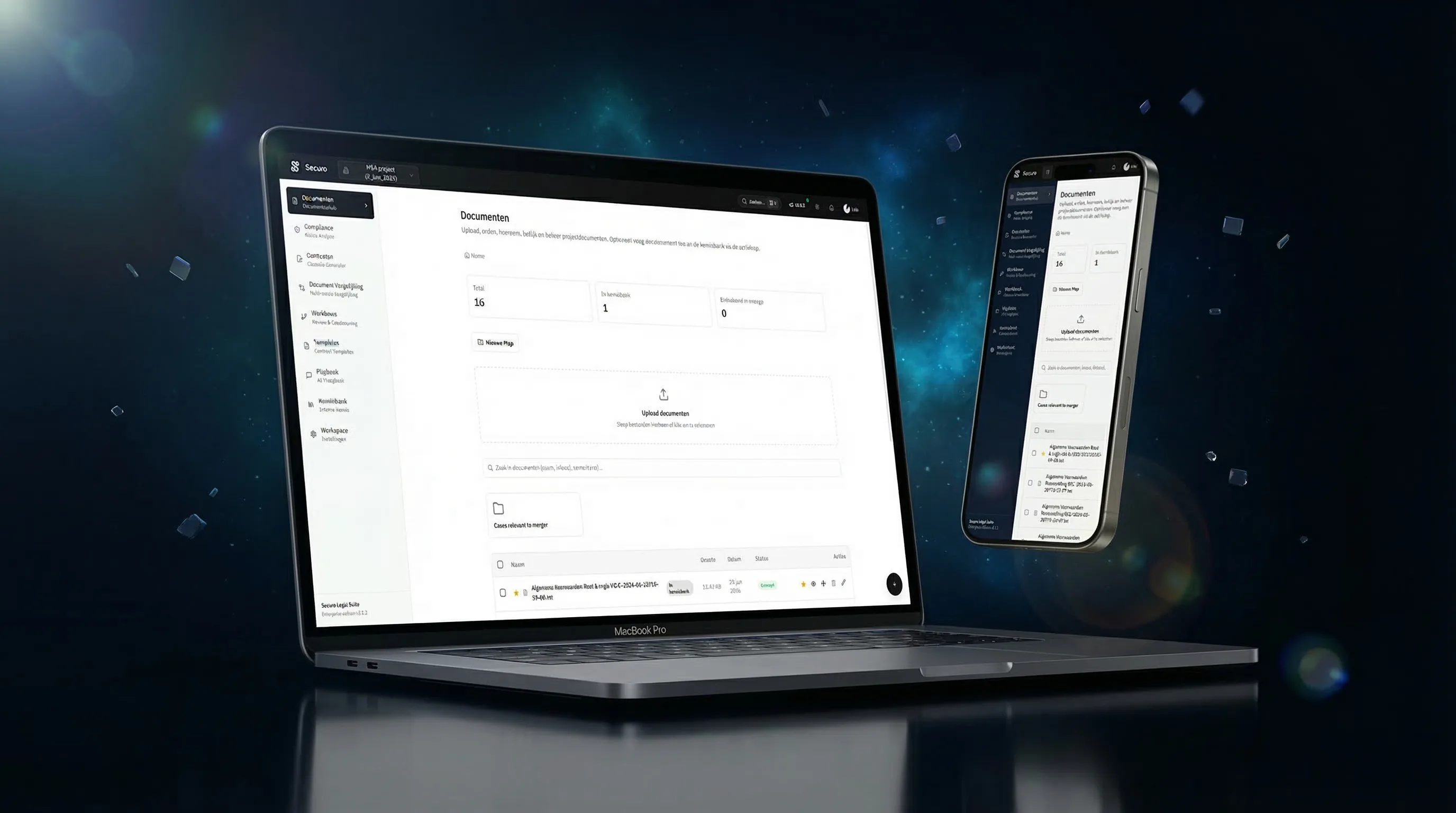
Root & Logic has engineered the Sovereign Gateway, an architectural framework designed specifically for maximum security, which we have deployed in production as the Securo platform.
This infrastructure acts as a highly fortified tollbooth between your internal network and the required AI computational engines.
Core Principles of the Gateway:
- 1Zero-Knowledge Processing: Your data is treated strictly as fuel for computation, not as memory to be stored. Once the AI generates a response, the context is immediately destroyed.
- 2Non-Training API Tunnels: We utilize highly specific, contractually guaranteed API endpoints where data retention and model training are explicitly disabled at the hardware provider level.
- 3European Data Residency: All processing routines and intermediate storage occur strictly within EU jurisdiction, utilizing sovereign European cloud providers or localized tenant architecture.
- 4Encryption at Every Layer: Data is encrypted both in transit and at rest, ensuring that even if physical infrastructure is compromised, the data remains entirely inaccessible.
This gateway approach allows organizations to deploy powerful AI Applications across their entire workforce, knowing that every query, document upload, and analysis is occurring within a walled garden.
The Illusion of Security: Common Pitfalls
When attempting to secure AI deployments, organizations frequently make critical architectural and policy errors:
* Relying on Terms of Service Updates: Believing that an email from a vendor stating "we care about your privacy" constitutes legal or technical protection. You must rely on physical architecture and API-level contractual guarantees, not marketing copy.
* The "Ban it All" Approach: Attempting to block all AI tools at the firewall level. This simply drives usage underground (Shadow AI) to personal devices, entirely removing your ability to monitor or control data flow.
* Ignoring RAG Vulnerabilities: When building internal knowledge bases using Retrieval-Augmented Generation, failing to implement strict access controls. If an intern prompts the AI to summarize the CEO's unreleased strategic plan, the AI will happily oblige if document-level permissions are not strictly enforced.
Fortify Your Data: Actionable Sovereignty Checklist
If your employees are using AI today, your data is already in motion. Take these immediate steps to establish sovereign control:
- [ ] Conduct a Shadow AI Audit: Survey your teams anonymously to understand which external AI tools they are currently using to process company data.
- [ ] Review API Contracts: If you are building internal software using external AI APIs, demand written confirmation of zero-day retention and non-training clauses.
- [ ] Implement an Internal Gateway: Deploy a secured, internal chat interface for your employees that routes requests through a non-training API tunnel, replacing their need to use public platforms.
- [ ] Validate Document Permissions: Ensure that any AI indexing your internal documents strictly honors the existing access control lists (ACLs) of your SharePoint or internal drives.
- [ ] Verify Physical Processing Locations: Audit where the actual GPU computation is taking place. Ensure the processing nodes are physically located within the EU.
Strategic Conclusion: The Business Case for Sovereignty
In an era where data has become the new frontline, sovereignty isn't paranoia—it's prudence.
Protecting your data does more than just satisfy compliance officers; it creates a distinct competitive advantage. When 78% of B2B buyers indicate that vendor data security practices significantly influence purchasing decisions, possessing a provably secure AI infrastructure becomes a powerful sales asset.
Furthermore, with IBM's 2024 Cost of a Data Breach Report placing the average incident cost at €4.45 million, investing in sovereign architecture is essentially a high-yield insurance policy.
Take control of your intellectual property today. Learn how RAG agents master your data without owning it, creating a perfectly secure internal knowledge system.
Want to build a walled garden for your company's intelligence? Contact Root & Logic for a confidential data sovereignty assessment.